 One of the many many new features of Microsoft Intune releases the last couple of months is the Intune App-Layer protection. In short, with Intune App-layer protection you are able to protect your corporate data with managed apps, in other words Mobile Application Management support is added to Microsoft Intune. But how do we manage apps with Microsoft Intune and what is possible? Let’s have a look in the next couple of blogs at what it is, which flavors are available and how you are able to set it up.
One of the many many new features of Microsoft Intune releases the last couple of months is the Intune App-Layer protection. In short, with Intune App-layer protection you are able to protect your corporate data with managed apps, in other words Mobile Application Management support is added to Microsoft Intune. But how do we manage apps with Microsoft Intune and what is possible? Let’s have a look in the next couple of blogs at what it is, which flavors are available and how you are able to set it up.
To start, while writing this, the features that are going to be described are currently only available in a Microsoft Intune standalone scenario.
Background
Allowing mobile devices connecting to your environment or corporate systems indirectly allows employees to access corporate data like email and do with it whatever they like. Copy data, forward it to the competition or save it to the device itself and after it gets stolen or lost the data will end up on the streets. Some companies doesn’t care because it cannot hurt them, but for more and more companies leaking data can be a huge issue.
Microsoft Intune now supports besides Mobile Device Management also Mobile Application Management, together with Microsoft Azure Rights Management and Microsoft Azure Active Directory Premium we call this comprehensive cloud solution the Microsoft Enterprise Mobility Suite. Read more background about the Microsoft Enterprise Mobility Suite here.
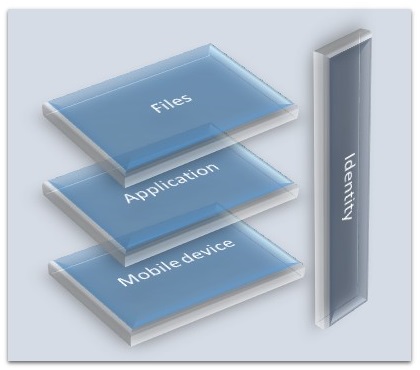
The Microsoft Enterprise Mobility Suite currently covers 4 layers of security, namely;
- Layer 1: Protecting at the mobile device (Mobile Device Management in Microsoft Intune).
- Layer 2: Protecting at the application (Mobile Application Management in Microsoft Intune).
- Layer 3: Protecting at the file on the device (Azure Rights Management Services).
- Layer 4: Protecting the identity and access (Azure Active Directory Premium).
In this series of blogs we are going to have a look at the Layer 2, protecting the application.
Supported features
Back to this small piece of the Enterprise Mobility Suite, Intune App-layer protection. This part of the series will cover the description of the features. Currently there are four paths to be able to manage your applications.
Office applications
Microsoft created Microsoft Office Apps that can be natively managed via MAM policies in Microsoft Intune. Those applications can be downloaded / provided from the App Stores. The following Microsoft Office Apps are currently available, for free:
- Word
- Excel
- PowerPoint
- OneDrive (for Business)
- Outlook Web App (OWA)
Intune companion apps
Microsoft Intune offers support for viewing content on the device via the following applications;
- Managed Browsers
- PDF Viewer
- AV Viewer
- Image Viewer
App Wrapping tool
With the app wrapping tool are you able to enable any application for management via Microsoft Intune, this is done without actually changing the code of the application. After you wrapped an application you cannot just deploy the application anymore but you need to first create a Mobile Application Management Policy. While deploying the app, you are able to associate the MAM policy with the deployment.
When using the Intune SDK, developers are also able to integrate their application for manageability.
Mobile Application Management Policies
So now that we know how to enable MAM for applications or Microsoft Intune App-layer protection you need to define and deploy the MAM policies. With those policies you are able to for instance prevent data relocation (copying, screen capturing or printing data from the app ), define which kind of apps can exchange data and prevent file backup to unauthorized locations.
More on this subject in one of my next blogs in this series in the upcoming weeks.
Have a nice day!
Update, more blogs in this series;
- Microsoft Intune App-layer – Microsoft Intune App Wrapping Tool
- Microsoft Intune App-layer – Manage your own App
- Microsoft Intune App-layer – Manage your own App Webcast


